Vision AI for defense & situational awareness
From surveillance feeds to satellite imagery. Build, deploy, and monitor computer vision models in air-gapped, on-premise environments.
Sovereign AI infrastructure for defense operations
Picsellia runs fully on-premise or air-gapped, connecting tactical sensors with centralized model management, training, and deployment.
Picsellia MLOps Platform
On-premise orchestration layer
Tactical Sensors
Connected devices running inference at the edge
Built for defense operations
From base security to battlefield intelligence, Picsellia powers vision AI workflows across defense and security operations.
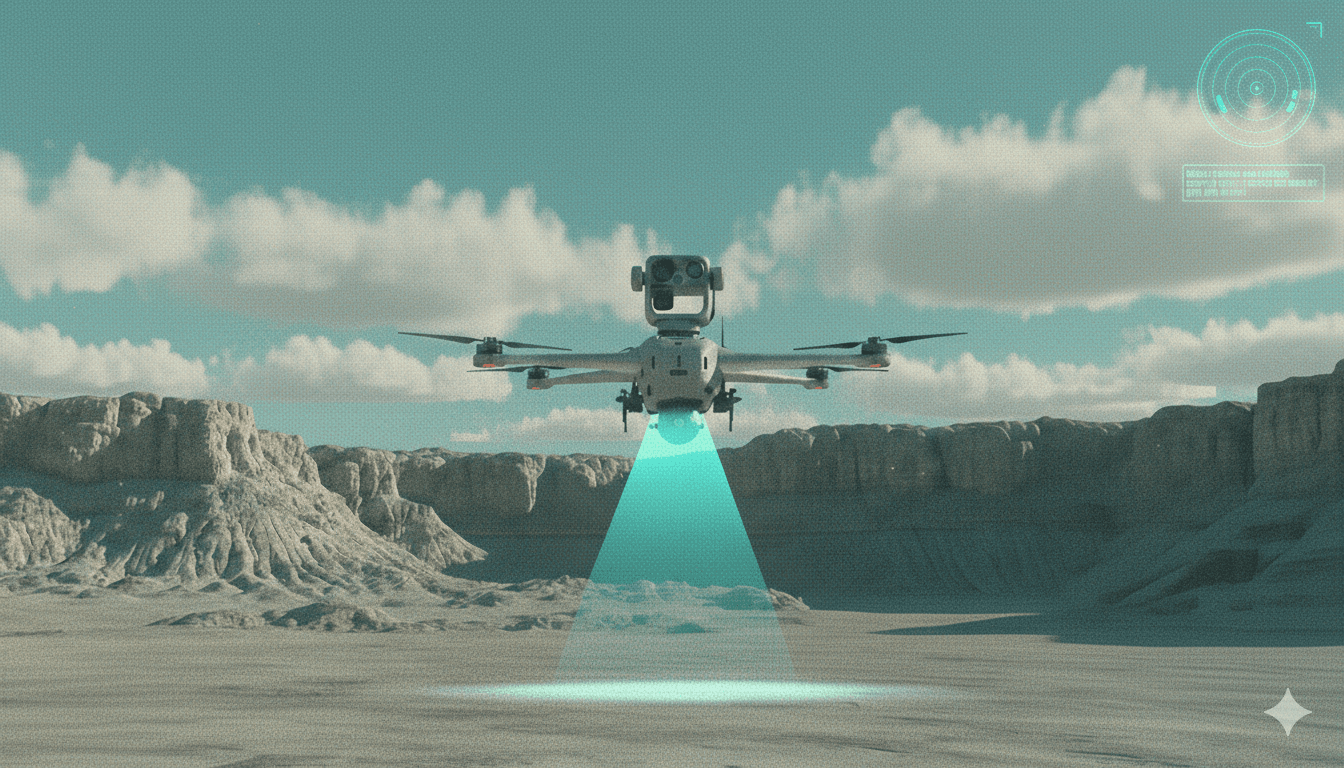
Threat Detection & Surveillance
Detect persons, vehicles, and unusual activity across camera networks. Real-time alerting for restricted zones and critical perimeters.
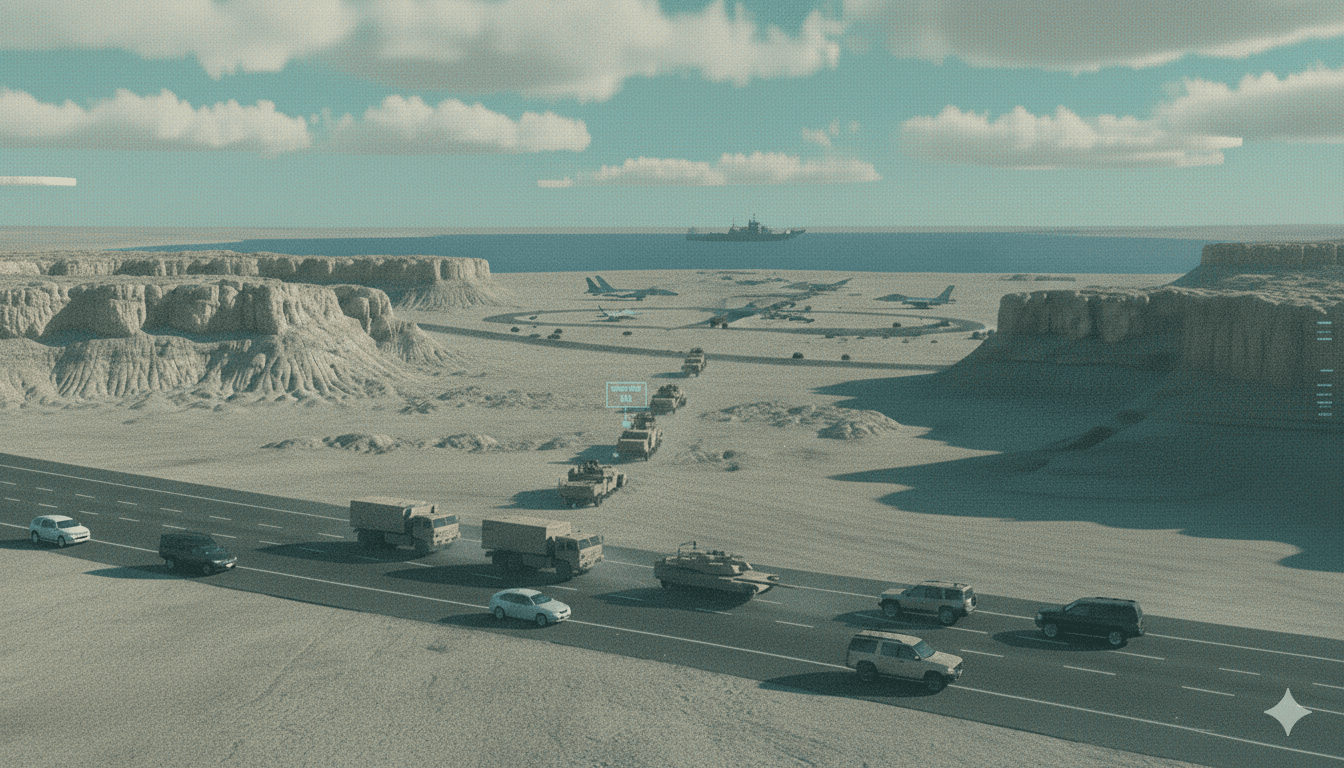
Vehicle & Asset Recognition
Classify and track military and civilian vehicles, aircraft, and naval vessels from satellite, aerial, and ground-level imagery.
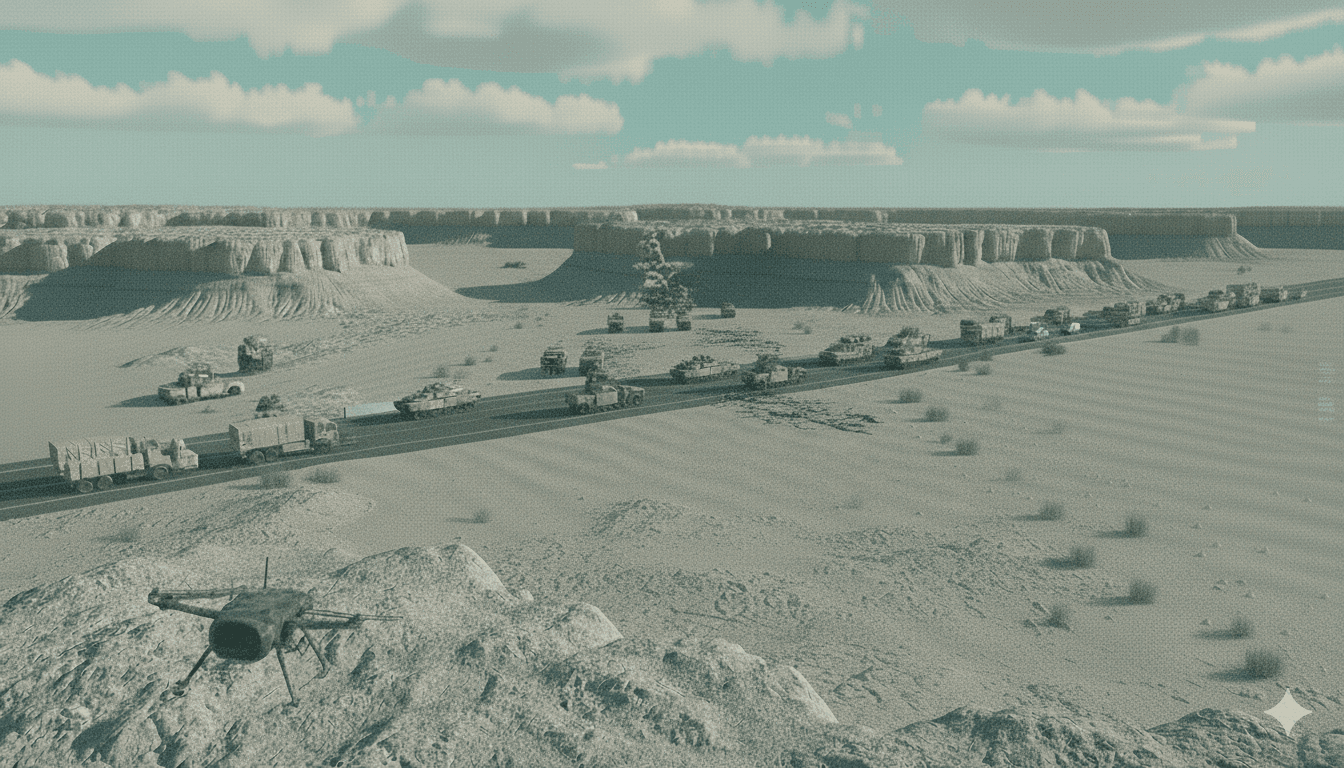
Terrain & Damage Assessment
Analyze satellite and drone imagery for terrain mapping, battle damage assessment, and infrastructure change detection.
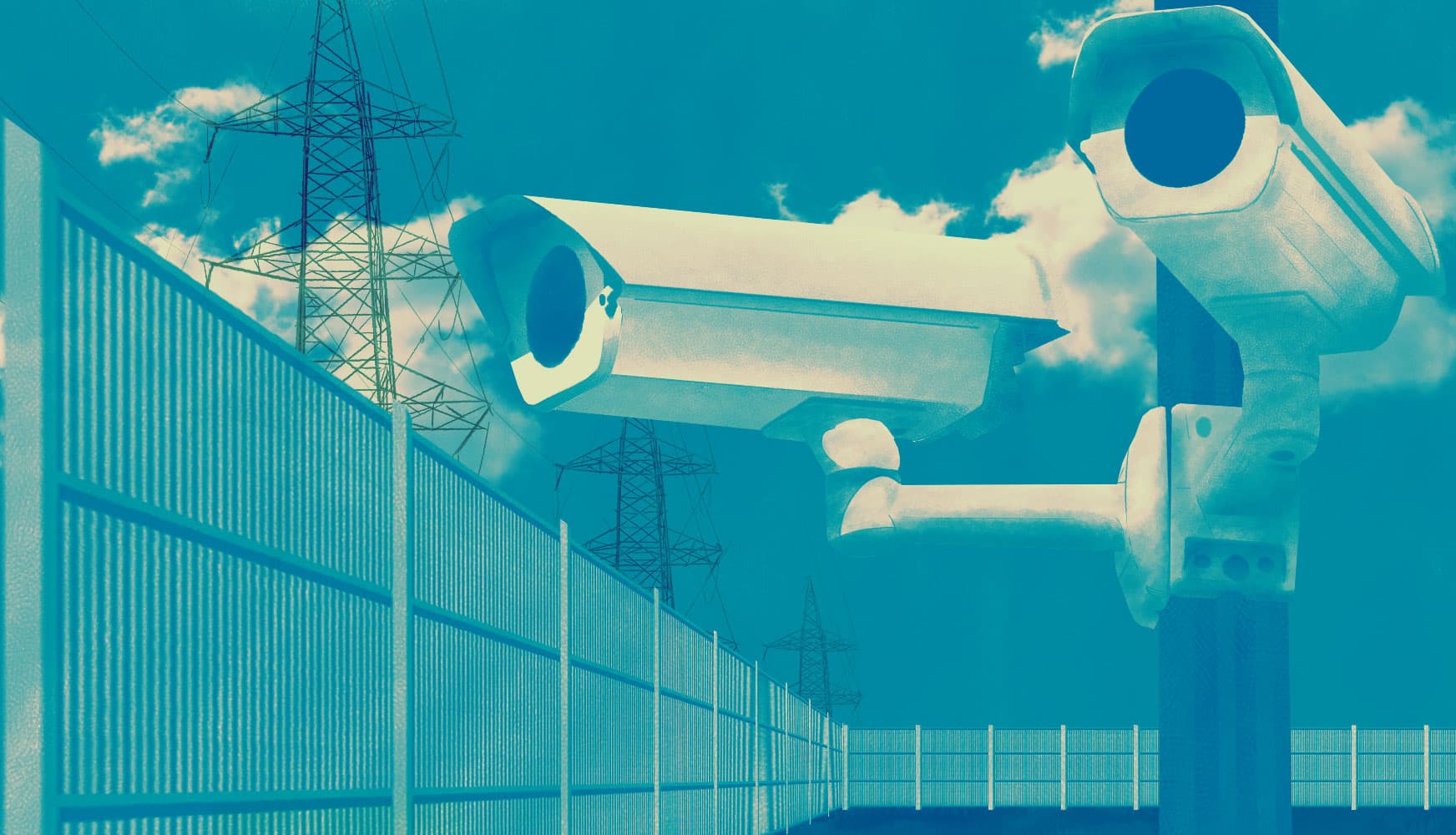
Perimeter Security
Automated intrusion detection for military installations, forward operating bases, and critical infrastructure facilities.
From raw intelligence to operational AI
Four steps to transform sensor data into deployed detection models with full sovereignty and traceability.
Centralize classified imagery
Aggregate data from surveillance cameras, UAVs, satellites, and tactical sensors into a secure, versioned repository within your own infrastructure.


Label targets with your analysts
Your intelligence analysts know what to look for. Capture that expertise by labeling objects of interest. AI pre-annotation accelerates the process by 10x.
Build detection models on-premise
Train models on your own GPU clusters without data ever leaving your network. Full experiment tracking and model versioning for reproducibility.

Deploy to tactical edge devices
Ship models to ruggedized edge hardware, drones, or on-premise servers. Monitor performance and retrain when operational conditions change.
The result? Sovereign AI for defense operations.
Built for defense-grade security
Defense operations demand the highest levels of data sovereignty, security, and operational control. Picsellia runs entirely within your infrastructure.
Air-Gapped Deployment
Operate in fully disconnected, classified environments
On-Premise Only
No data leaves your network, ever
ISO 27001 Certified
Enterprise-grade security and data protection
Full Audit Trail
Every action logged for compliance and accountability
Role-Based Access
Clearance-level permissions for teams and operators
Data Sovereignty
Your data never leaves your perimeter
Ready to deploy sovereign vision AI?
See how defense organizations use Picsellia to build and deploy computer vision models in secure, air-gapped environments.